The Iso 27001 Risk Assessment Spreadsheet Cover Up
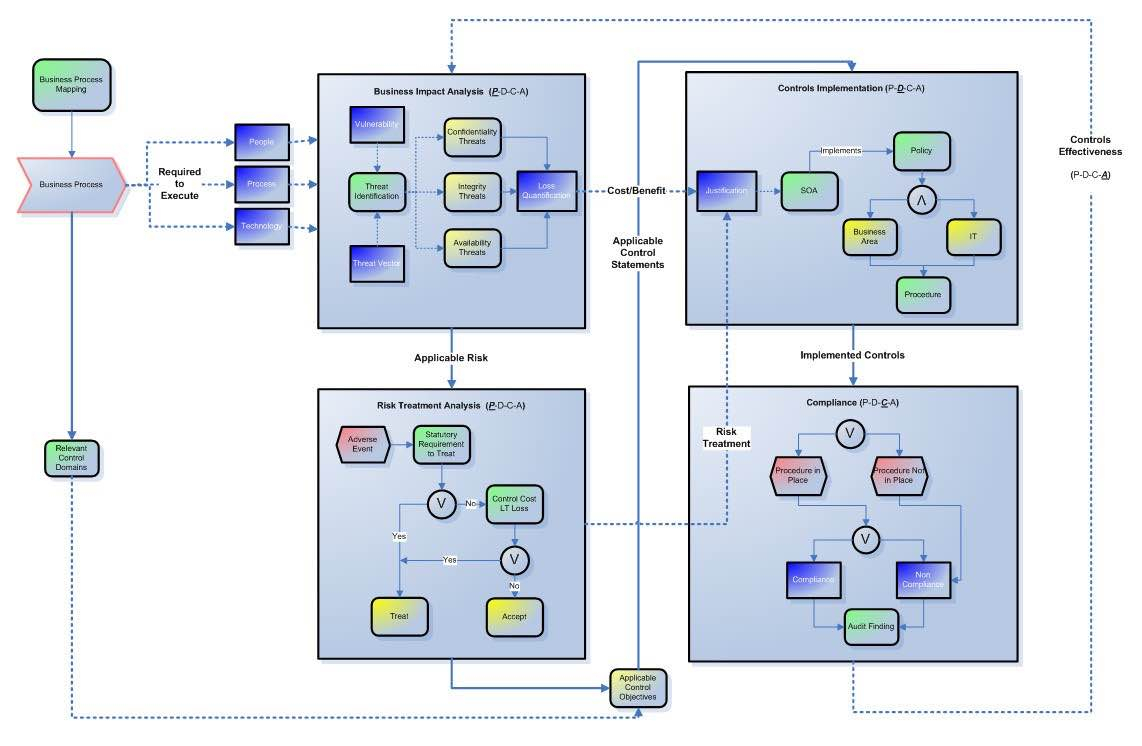
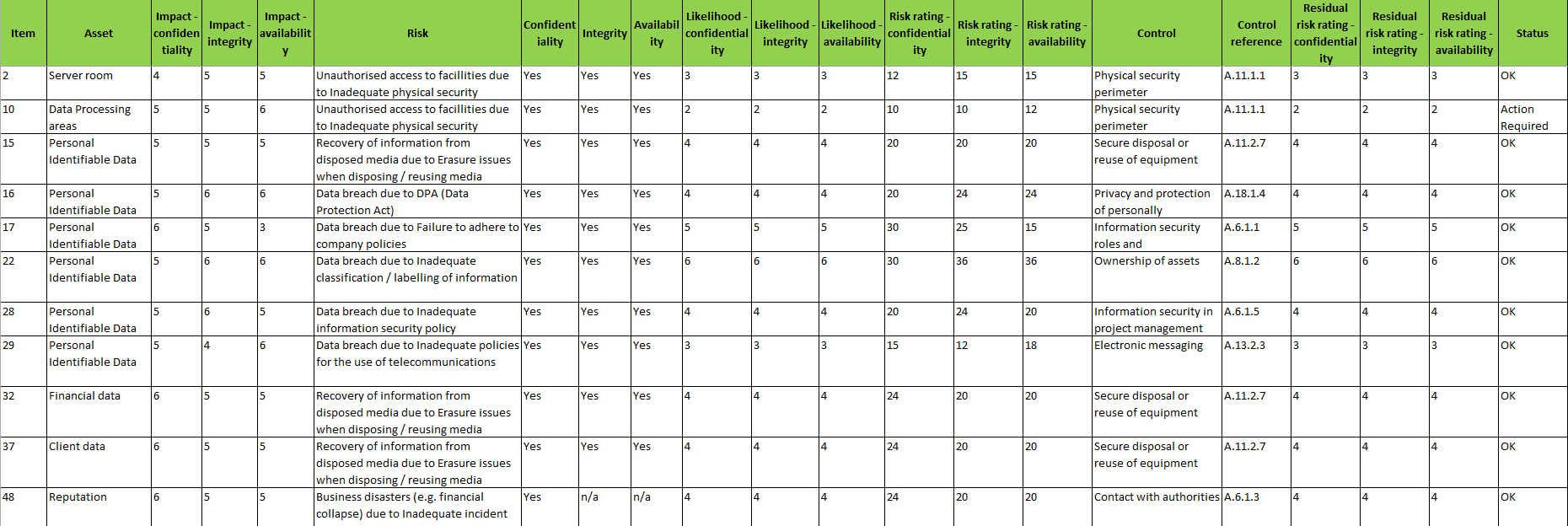
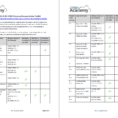
Whatever varieties of assessment you decide on, it’s important to understand about security risks assessment templates. The ones working on it would also have to monitor different things, besides the assessment. Risk assessment analyzes threats together with vulnerabilities and current controls. It is a very basic practice which is done by every organization or business group, in a way to avoid any loss. With ISO 27001, it’s imperative to use a reliable method to define and establish a thorough risk assessment.
Risk assessment is a significant step in protecting yourself, your company and others, along with complying with the law. It is primarily a business concept and it is all about money. A NIST risk assessment is not any different in concept than every other.
The Honest to Goodness Truth on Iso 27001 Risk Assessment Spreadsheet
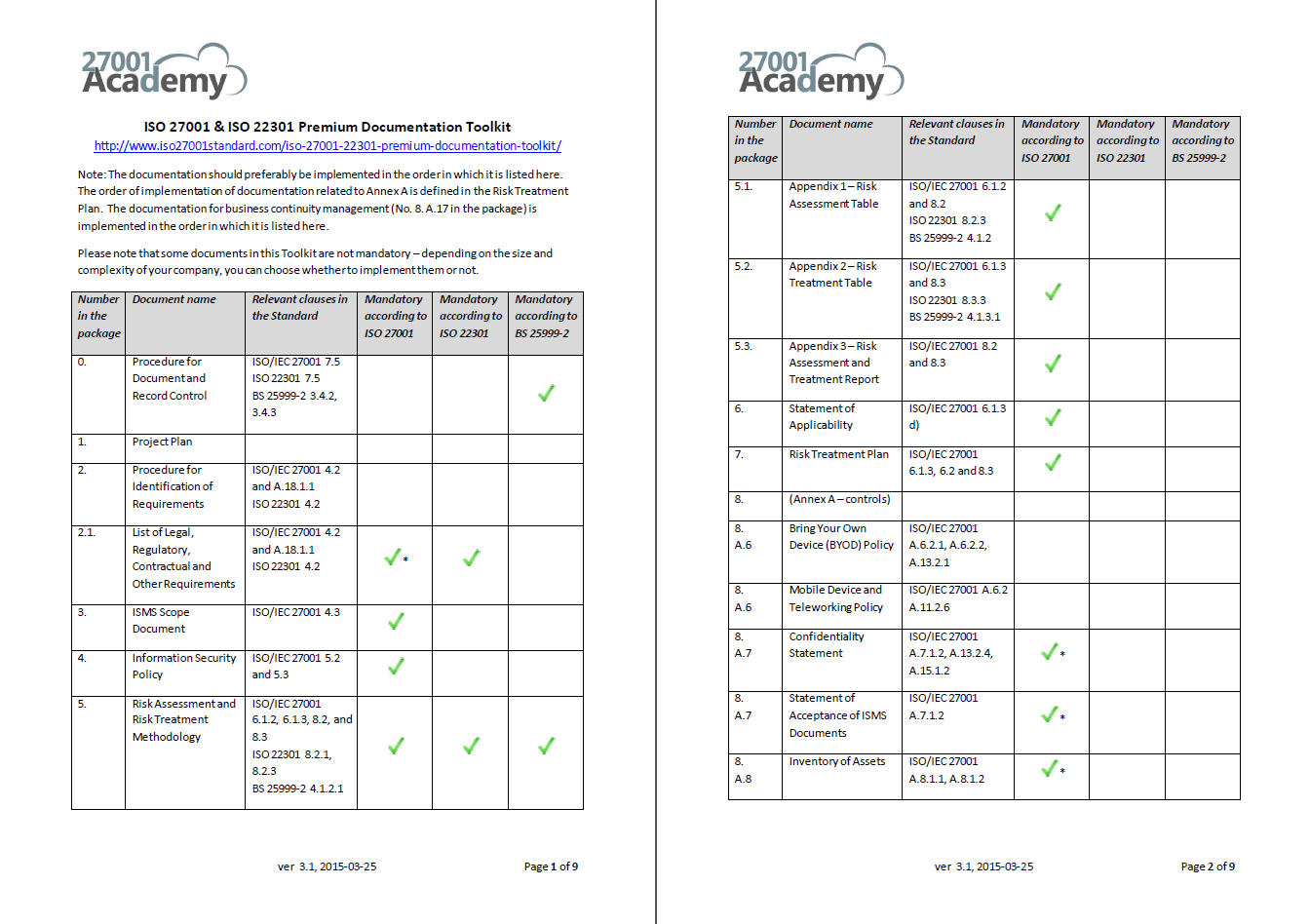
ISO 27002 is a thorough document indeed, thus selecting the correct controls and relevant control clauses is vital for implementing an ISMS. ISO 27001 isn’t the very same as the standards it replaces. To embark on the path to becoming ISO 27001 accredited, the very first thing you have to do is decide which elements of your business you wish to include in the accreditation.
If it comes to cyber risks, organizations can’t afford to have a wait-and-see strategy. By way of example, suppose you need to estimate the risk related to the threat of hackers compromising a specific system. Risk isn’t a straightforward idea. Some risks can have a high probability, but an extremely low effects. Determine what you should do to tackle the risks and opportunities that could influence the potency of your organization’s ISMS or disrupt its operation.
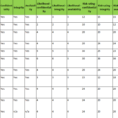
You will probably be unaware of a lot of the risks, but they have the capability to cause considerable operational, reputational and financial impact if they’re not correctly identified, controlled and mitigated. You should likewise be able to analyse risks on the basis your baseline security controls are in place and effective. Risks could be measured by internal analysis of the company or sometimes external organizational analysis may also be carried out. Although identifying risks is relatively straightforward, it’s frequently the most time-consuming portion of the whole risk assessment procedure. In the more general scenario, every probable risk may have a pre-formulated plan to manage its possible consequences (to guarantee contingency in the event the risk becomes a liability).
In any instance, you should not begin assessing the risks before you adapt the methodology to your unique conditions and to your requirements. It is very important to assess risk in respect to natural disasters like floods, earthquakes, etc. Risk can be described as a prospective event which can be expressed regarding consequence, impact, or seriousness of the impact and its related odds of occurrence. Risks affecting organizations can have consequences with respect to financial performance and expert reputation, in addition to environmental, safety and societal outcomes.
If not one of the options above suits your profile you may use the info in my course for awareness on information security and get to understand what are the security requirements that all these organizations around the world have chosen to adopt. There are many techniques to collect the info you should assess risk. If you opt not to present certain information, we might not have the ability to provide requested services. In case you want to produce your document more secure, you might also convert excel to PDF to keep the misuse of the data in the dictionary. Our BCDRP document comprises all appropriate information for helping you effectively document all essential measures in case of a disaster.
Introducing Iso 27001 Risk Assessment Spreadsheet
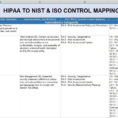
Looking at NIST CSF, you can observe that the informative references encompass a wide array of standards. If you’re using a variety of standards to help mitigate security risks then you are going to have to be in a position to discover the suitable documentation. If you’ve been certified to a different ISO standard, you’ll already understand what’s involved with defining the range of your quality management system. The standard isn’t prescriptive about which ought to be used. Accordingly, you must define a standard for specifying the significance of each asset.
Project risk management has to be considered at the various phases of acquisition. Therefore, operational risk management is a crucial portion of the total risk strategy, contributing to various different elements like ERM and compliance that are key characteristics of the GRC framework. For the offshore gas and oil business, it is regulated by the safety case regime in many countries.
Make a determination on whether you would like to delete the Management Procedures or not. For any encrypted file to be decrypted an important should be communicated first and any essential management procedures want to guarantee that the origin of the key is trustworthy. It’s possible that different small business lines or processes have various wants and risk tolerances. When the necessary processes are implemented, now is the time to appraise and see whether the business has reached the predefined outcomes.
Sample for Iso 27001 Risk Assessment Spreadsheet